Featured Resources
How to Create a BYOD-Friendly Data Loss Prevention Policy


March 13, 2025
Blog
How to Create a BYOD-Friendly Data Loss Prevention Policy
Creating and implementing a data loss prevention policy is a critical security measure for organizations today. But many DLP policies prioritize security at the cost of usability, which leads to employee frustration and, in turn, security workarounds–ultimately increasing the risk of data leaks and shadow IT. Achieving this balance is challenging, as implementing DLP policies […]
BYOD Security: Managing Third-Party Risk


February 18, 2025
Blog
BYOD Security: Managing Third-Party Risk
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency


December 17, 2024
Blog
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency
5 Myths About Remote Work Security: What Every IT Leader Should Know


June 12, 2024
Blog
5 Myths About Remote Work Security: What Every IT Leader Should Know
An Evolution of Secure BYOD and Remote Work
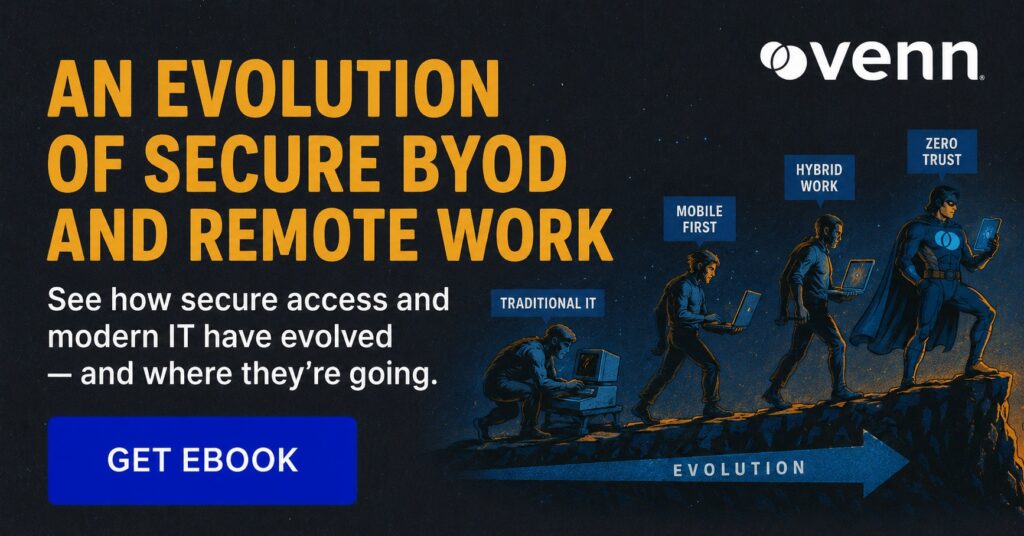
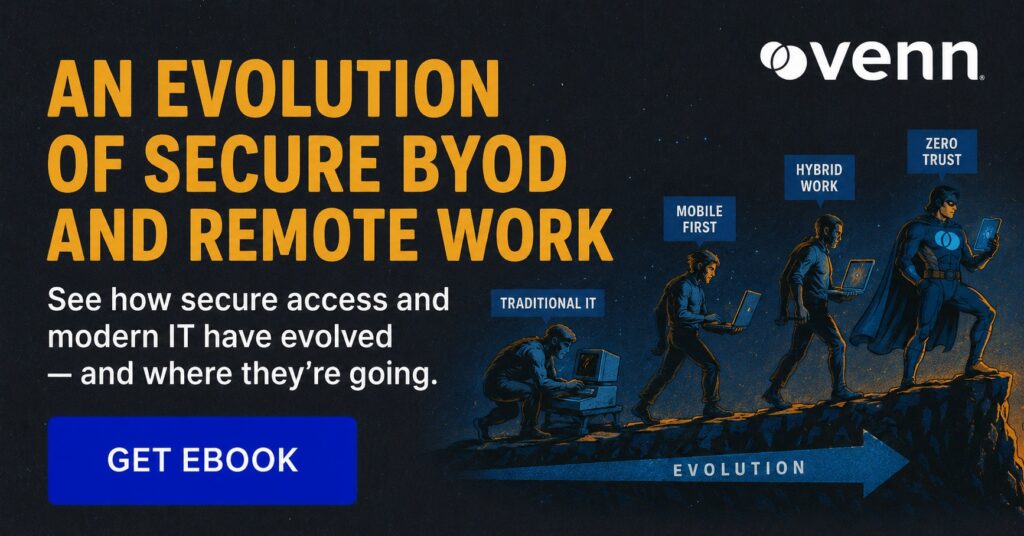
Whitepaper
An Evolution of Secure BYOD and Remote Work
What you’ll learn An independent perspective on how Blue Border™ bridges the gap between UEM/MDM and VDI – so IT teams can securely enable contractors, offshore teams and remote employees to work on their personal laptops. Who this report is for IT and security leaders supporting: remote employees, contractors, offshore teams, and BYOD policies – […]
NIST AI Risk Management Framework: 4 Components and Best Practices


Knowledge Article
NIST AI Risk Management Framework: 4 Components and Best Practices
What Is the NIST AI Risk Management Framework (NIST AI RMF)? The NIST AI Risk Management Framework (AI RMF 1.0), released in January 2023, is a voluntary guidance designed to help organizations design, develop, and use AI systems responsibly. It promotes trustworthy AI by managing risks related to safety, fairness, bias, and security across the […]
What Is Shadow AI, Why It’s Growing and What You Can Do About It
Knowledge Article
What Is Shadow AI, Why It’s Growing and What You Can Do About It
What Is Shadow AI? Shadow AI refers to the unauthorized, unapproved, or unmonitored use of Artificial Intelligence tools (like ChatGPT, Claude, or Gemini) by employees within an organization. This poses significant data security risks, including intellectual property leakage, regulatory noncompliance (GDPR, HIPAA), and increased attack surfaces. It is an evolution of shadow IT, driven by […]
VDI Challenges for a Secure Remote Workforce: What the Data Says


May 7, 2026
Blog
VDI Challenges for a Secure Remote Workforce: What the Data Says
Organizations have relied on virtual desktop infrastructure for decades to secure remote access to company data. The logic made sense: put everything in a centralized virtual desktop, control the environment, and your endpoints become largely irrelevant. But that logic was built for a different era of work; one where most employees used company-issued devices, worked […]
Venn Wins Gold in Three 2026 Cybersecurity Excellence Awards Categories


Press Release
Venn Wins Gold in Three 2026 Cybersecurity Excellence Awards Categories
NEW YORK–(BUSINESS WIRE)–Venn, the secure remote work company, today announced it earned Gold in three categories of the 2026 Cybersecurity Excellence Awards, including Secure Remote Access, Endpoint Security and Excellence in Cybersecurity Innovation for its patented Blue Border™ technology. The recognition highlights Venn’s innovation in helping organizations securely enable remote work. The Cybersecurity Excellence Awards […]
What Are AI Governance Solutions? A Practical Guide for IT Leaders
Knowledge Article
What Are AI Governance Solutions? A Practical Guide for IT Leaders
AI governance has become a market category almost overnight. The global AI governance market was valued at $308 million in 2025 and is projected to reach $3.59 billion by 2033 – a 36% annual growth rate driven by regulatory pressure, rising shadow AI risk, and boards demanding accountability for how AI tools interact with company […]
AI Governance Framework: The Endpoint Problem Most Organizations Miss


Knowledge Article
AI Governance Framework: The Endpoint Problem Most Organizations Miss
Most organizations now have some version of an AI governance framework. There’s a policy document somewhere, a list of approved tools, maybe a committee reviewing new requests. The problem isn’t the framework. It’s that for organizations with remote employees and contractors working from personal devices, the framework has no way to enforce itself. AI tools […]
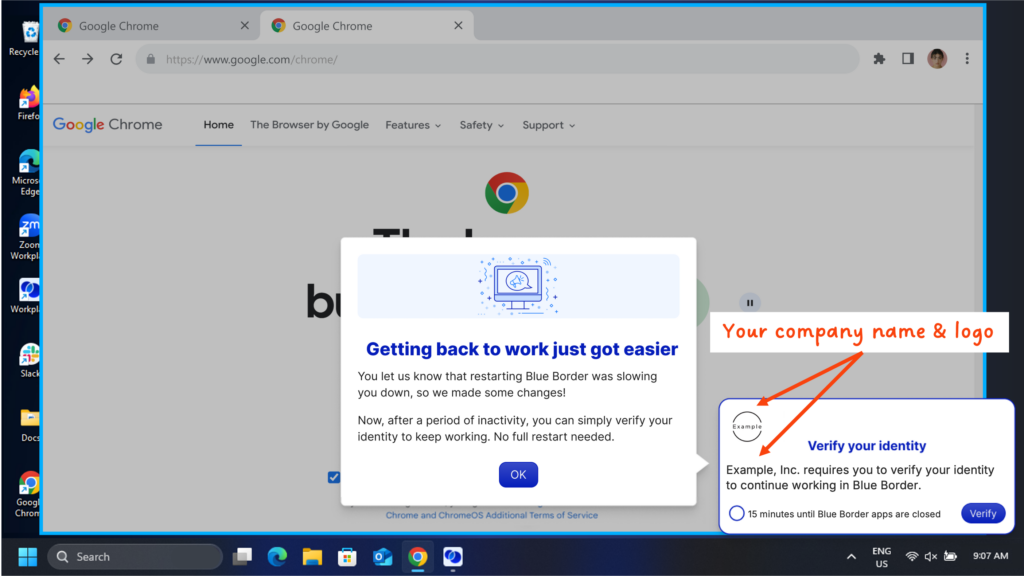
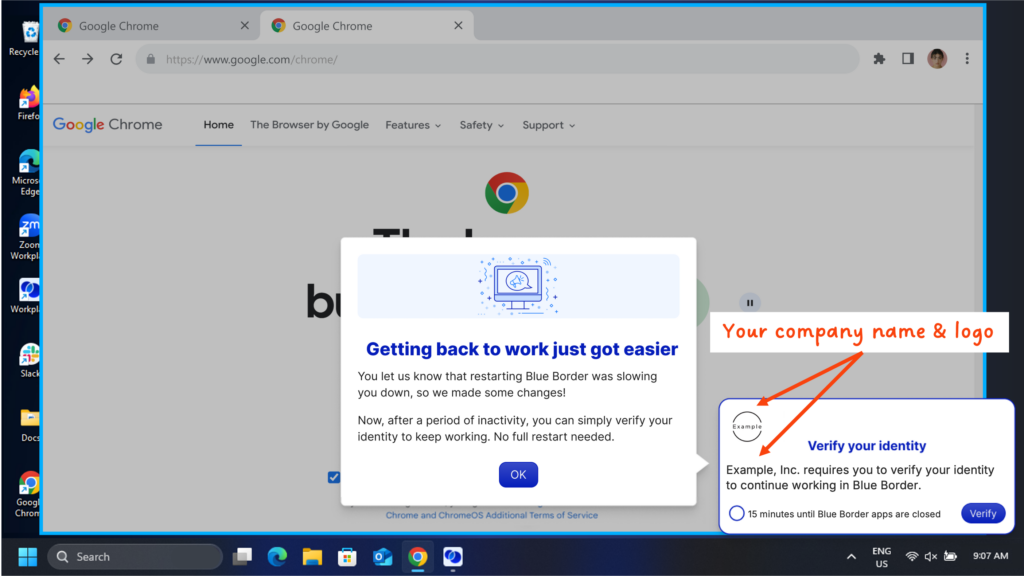
We Kept Hearing the Same Complaint. The Solution Was Re-Auth.
May 4, 2026
Blog
We Kept Hearing the Same Complaint. The Solution Was Re-Auth.
There’s a version of product management where you build things because they’re technically impressive, or because they fit neatly into your roadmap, or because a big customer asked for them. That version is tempting. It’s also usually wrong. The best features start somewhere simpler: you found out your product was adding friction to someone’s morning […]
AI Data Protection: What IT Leaders Need to Know in 2026


Knowledge Article
AI Data Protection: What IT Leaders Need to Know in 2026
Most organizations approaching AI data protection are asking the wrong question. They want to know how to secure the AI tools themselves — the models, the APIs, the enterprise licenses. That is a reasonable concern. But the more immediate exposure is what flows into those tools: client contracts, financial records, proprietary source code, protected health […]