Top 12 Endpoint Security Solutions and How to Choose

What Are Endpoint Security Solutions?
Endpoint security solutions protect user devices (laptops, phones, servers) from cyber threats like malware, ransomware, and phishing by providing advanced prevention, detection, and response, often through Endpoint Protection Platforms (EPP) (antivirus, firewall) and Endpoint Detection & Response (EDR) (behavioral analysis, investigation) managed centrally.
Key vendors include remote work solutions like Venn and IBM MaaS360, and endpoint security solutions like CrowdStrike Falcon and SentinelOne Singularity Endpoint, offering features like AI-driven threat hunting, zero-day protection, and centralized visibility for IT teams to secure devices in complex environments.
Key types of endpoint security:
- Remote work solutions: Support distributed teams via cloud-based infrastructure, secure workspaces, and remote access platforms.
- Endpoint protection platforms (EPP): Baseline defense with antivirus, anti-malware, and firewalls to prevent known threats.
- Endpoint detection and response (EDR): Focuses on detecting and responding to advanced threats using behavioral analytics and threat hunting.
- Extended detection and response (XDR): Integrates endpoint data with other security layers (network, cloud, email) for broader visibility.
- Managed detection and response (MDR): Outsources management of endpoint protection to a service provider with expertise.
Better Endpoint Security for Contractors – on Unmanaged Devices
Discover the top solutions for providing secure remote access to contractors on unmanaged laptops. No shipping hardware, no VDI.

In this article:
How Endpoint Security Differs from Traditional Antivirus
Traditional antivirus software focuses primarily on detecting and eliminating known malware using signature-based detection. This method involves scanning files and processes for patterns that match a database of recognized threats. While effective against established viruses and malicious code, antivirus alone struggles to keep up with emerging threats and advanced attacks, such as zero-day exploits, fileless malware, or ransomware variants that rapidly evolve beyond static signatures.
Endpoint security solutions offer a much broader defense. They combine antivirus engines with behavioral analysis, machine learning, and threat intelligence to uncover suspicious activity even when no known malware signature is present. Endpoint security products also include features like device management, policy enforcement, vulnerability assessment, and automated incident response. By integrating multiple layers of protection and analysis, endpoint security counters a wide spectrum of threats, providing more complete coverage for modern enterprise environments.
Key Types of Endpoint Security Solutions
Remote Work Solutions
Remote work solutions combine multiple technologies to support distributed teams. Modern environments rely on cloud-based infrastructure, secure workspaces, remote access platforms, collaboration tools, and workforce management systems. Instead of depending only on VPNs and email, organizations now use integrated platforms that provide secure access to applications, centralized communication, and scalable cloud resources.
These solutions typically fall into several categories. Secure workspace and remote desktop tools isolate or deliver work environments securely. Remote access platforms use identity-based controls and zero-trust approaches to limit exposure. Collaboration and project management tools centralize communication and task tracking, while workforce management systems handle scheduling, compliance, and productivity monitoring.
Endpoint Protection Platforms (EPP)
Endpoint Protection Platforms (EPP) are comprehensive security suites that provide a centralized set of tools aimed at preventing malware, ransomware, and other malicious activities on endpoint devices. EPP solutions typically include antivirus, anti-malware, personal firewalls, and device control features all managed from a single interface.
They harness traditional signature-based detection while integrating more advanced techniques like heuristic analysis and sandboxing to identify unknown threats. The main goal of EPP is to block threats before they infiltrate endpoint devices and the wider network. EPP is widely adopted in enterprises for its ease of deployment and management, especially in environments with diverse devices and operating systems.
Endpoint Detection and Response (EDR)
Endpoint Detection and Response (EDR) solutions go beyond prevention, focusing on detecting, investigating, and responding to advanced threats that evade traditional defenses. EDR tools continuously monitor endpoint activity, collecting detailed telemetry such as process creation, file modification, and network connections.
When suspicious activity is detected, EDR provides analysts with rich contextual data and forensics to trace the origin, timeline, and impact of threats, enabling more precise containment and remediation. EDR equips security teams to perform proactive threat hunting and alerts them to indicators of compromise even if the attack payload is novel or fileless.
Extended Detection and Response (XDR)
Extended Detection and Response (XDR) builds upon the foundations of EDR by aggregating security data not just from endpoints, but from across the entire IT environment: servers, cloud workloads, email, and network traffic. XDR platforms correlate signals from these diverse sources to improve detection accuracy, eliminate visibility blind spots, and simplify investigation workflows.
By unifying security telemetry, XDR helps security teams piece together multi-stage attacks that would otherwise evade isolated security tools. Beyond detection, XDR automates response actions across multiple domains. For example, when an endpoint alert is triggered, XDR can simultaneously update email security rules, block malicious domains at the firewall, and quarantine affected files in the cloud.
Managed Detection and Response (MDR)
Managed Detection and Response (MDR) services take endpoint protection further by providing outsourced security operations and expertise. With MDR, a third-party provider continuously monitors, investigates, and responds to threats on behalf of the organization, leveraging a combination of EDR, threat intelligence, and human analysis.
This approach enables organizations without sizable in-house security teams to access advanced capabilities and around-the-clock protection. MDR providers also help organizations respond rapidly to incidents by delivering tailored guidance, hands-on remediation, and post-incident analysis. They offer actionable intelligence to improve overall security posture and can adapt coverage as the threat landscape changes.
Notable Endpoint Security Solutions
Remote Work Solutions
1. Venn

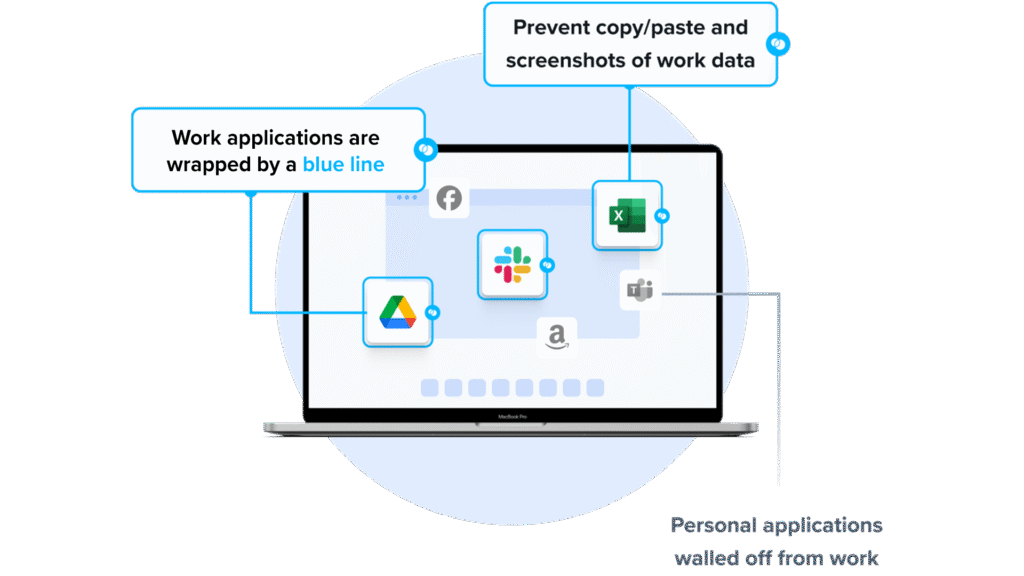
Venn’s Blue Border™ delivers endpoint security for BYOD computers used by contractors and remote employees. Similar to an MDM solution but purpose-built for laptops, company data and applications reside in a Secure Enclave installed on the user’s PC or Mac. Within this environment, all data is encrypted, access is controlled, and business activity is clearly marked by Blue Border™ — ensuring corporate data is protected while personal use remains private.
Security controls include:
- Blocking copy/paste between work and personal apps
- Restricting file downloads and use of external storage
- Preventing or watermarking screenshots
- Enforcing consistent protections across both browser-based and local applications
With Venn, organizations can extend enterprise-grade endpoint security to unmanaged devices, reducing risk without sacrificing user experience or productivity.
You can book a quick demo here.
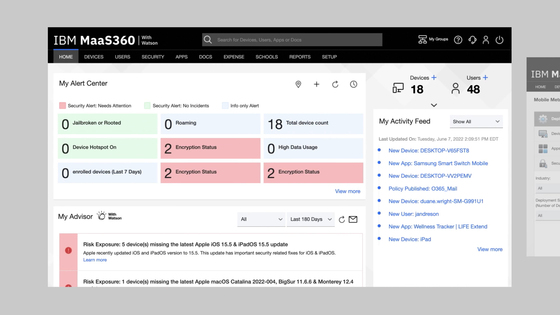
2. IBM MaaS360

IBM MaaS360 is a unified endpoint management (UEM) platform to manage and secure mobile devices and laptops from a centralized console. It provides built-in security controls, AI-driven analytics, and automated policy enforcement to support hybrid and frontline workforces. The platform enables organizations to configure devices, manage applications, and maintain compliance through a single dashboard.
Key features include:
- Unified endpoint management: Manage smartphones, tablets, and laptops from one console
- AI-driven analytics: Uses AI insights to identify risks and provide policy recommendations
- Identity management: Controls user access and enforces authentication policies
- Granular patch management: Supports controlled patching and updates across managed devices
- Mobile threat management: Detects and mitigates mobile-specific threats
- Containerization: Separates business and personal data for privacy and compliance
Source: IBM
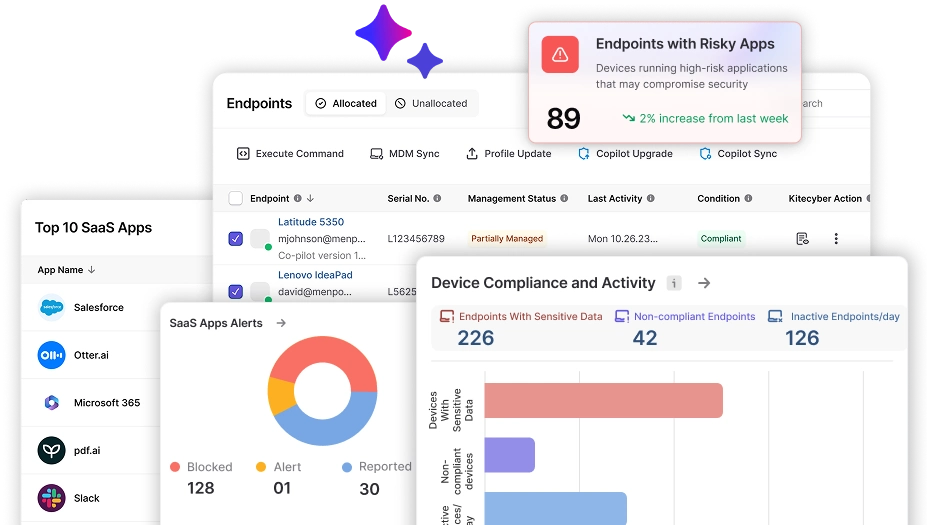
3. Kitecyber

Kitecyber provides BYOD security by combining endpoint management, zero trust access, and data protection controls into a single platform. It focuses on protecting corporate data on personal devices without intrusive monitoring. The solution includes secure remote access, data loss prevention, secure web gateway capabilities, and real-time threat detection using AI models that operate directly on endpoints.
Key features include:
Zero trust enforcement: Verifies device compliance before granting access to corporate resources- Data loss prevention (DLP): Scans devices for sensitive data and enables remote encryption or deletion
- Secure web gateway: Blocks malicious websites and ransomware threats before users interact with them
- Endpoint management: Manages Windows, macOS, and Linux devices through a unified console
- Real-time threat detection: Uses multi-model AI to detect phishing, identity theft, and data exfiltration attempts at the moment of interaction
- Secure remote access (VPN): Establishes encrypted connections between users and corporate networks
Source: Kitecyber
Endpoint Security Solutions
4. CrowdStrike Falcon

CrowdStrike Falcon is an AI-driven endpoint security solution to detect, prevent, and respond to threats. It combines threat intelligence, machine learning, and behavioral analytics to defend against known and unknown attacks, including fileless malware, ransomware, and lateral movement.
Key features include:
- Single lightweight sensor: Deploys in minutes and protects across all major operating systems with minimal performance impact
- AI-powered detection and response: Uses behavioral analytics and adversary intelligence to identify stealthy threats and automate remediation
- Charlotte AI: Agentic AI that triages alerts, investigates incidents, and drives autonomous response actions
- Cross-domain visibility: Detects threats across endpoints, cloud workloads, and network layers for unified protection
- CrowdStrike Signal: Builds host-specific AI models to detect subtle, early-stage attack behaviors
Source: CrowdStrike Falcon
5. SentinelOne Singularity Endpoint

SentinelOne Singularity Endpoint delivers AI-powered protection, detection, and response across endpoint and identity surfaces through a single platform. It defends against fast-moving threats using on-device machine learning and behavioral AI, without relying on cloud connectivity or human intervention.
Key features include:
- Autonomous AI-based protection: Uses static and behavioral AI on-device to prevent malware, ransomware, and zero-day threats in real time
- Real-time threat detection: Identifies anomalous behaviors and system-level or identity-based attacks without human input
- Automated remediation: Supports 1-click or automated rollback to remove threats and restore systems with minimal disruption
- Storyline® correlation engine: Automatically links related events into attack narratives, providing real-time context and reducing investigation time
- Unified lightweight agent: Delivers EDR and identity protection across Windows, macOS, and Linux with minimal performance impact
Source: SentinelOne
6. Bitdefender GravityZone

Bitdefender GravityZone Business Security is a unified endpoint protection solution that delivers layered defense against ransomware, phishing, zero-day attacks, and network-based threats. It combines machine learning, behavioral analysis, and continuous process monitoring to detect and stop threats.
Key features include:
- Multi-layered threat protection: Combines machine learning, behavior monitoring, and process inspection to detect and block known and unknown threats
- Ransomware mitigation: Identifies abnormal encryption activity, blocks malicious processes, and restores files using automatic rollback
- Network attack defense: Monitors incoming, outgoing, and lateral traffic to stop brute force, password theft, and other network-based attacks
- Risk management module: Identifies risky user behavior and system misconfigurations, prioritizes exposure, and guides remediation
- Web and content filtering: Inspects web traffic (including SSL), blocks phishing attempts, and controls access to websites and applications
Source: Bit Defender
7. Sophos Endpoint

Sophos Endpoint is an AI-powered security solution that protects against ransomware, data loss, and cyberattacks across desktops, servers, and mobile devices. It combines deep learning models, behavioral analysis, and anti-exploit technology to stop threats before they cause harm. Sophos Endpoint is managed through Sophos Central, a unified cloud-based platform that simplifies administration with recommended settings enabled by default.
Key features include:
- Prevention-focused AI engine: Uses deep learning to detect both known and unknown threats before they execute
- CryptoGuard anti-ransomware: Blocks malicious encryption activity and automatically rolls back affected files
- Adaptive attack protection: Activates stronger defenses in real time when hands-on-keyboard activity is detected
- Critical attack warning system: Notifies all administrators of large-scale threats across multiple devices
- Remote ransomware defense: Detects and stops encryption attempts from unmanaged or compromised devices on the network
Source: Sophos
8. Trend Micro Vision One

Trend Micro Vision One is an AI-enabled cybersecurity platform that helps organizations predict, prevent, and respond to threats. It centralizes cyber risk exposure management, layered threat protection, and security operations, providing visibility across endpoints, cloud workloads, networks, identities, and email.
Key features include:
- Unified security platform: Integrates endpoint, cloud, network, email, and identity protection into a single view for centralized control
- Cyber Risk Exposure Management (CREM): Continuously monitors and prioritizes risks based on potential business impact
- Proactive AI capabilities (Trend Cybertron): Detects and predicts threats before exploitation using specialized AI models
- Context-rich detection: Provides detailed insights to correlate events and accelerate investigation and response
- AI-powered threat hunting: Automates detection and analytics to improve visibility and efficiency in SecOps workflows
Source: Trend Vision One
9. ThreatLocker Detect

ThreatLocker Detect is a policy-based EDR solution to identify and respond to cyber threats across an organization’s environment. Unlike AI-reliant EDR tools, ThreatLocker Detect allows IT teams to define custom rules that govern what behaviors trigger alerts or automated responses. It continuously monitors telemetry from other ThreatLocker modules and system logs.
Key features include:
- Policy-based detection engine: Enables customizable, transparent rules to identify and act on Indicators of Compromise (IoCs)
- Real-time local enforcement: Security policies are evaluated and enforced directly on endpoints in milliseconds, regardless of internet connectivity
- Automated incident response: Supports responses such as alerts, system isolation, and Lockdown Mode to block all activity on compromised devices
- ThreatLocker community sharing: Access and contribute to a shared repository of detection policies aligned with MITRE and CISA guidance
- Microsoft 365 integration: Monitors cloud activity for risks like impossible travel, anonymous sign-ins, and compromised devices using Graph API logs
Source: ThreatLocker
10. Barracuda XDR

Barracuda XDR Endpoint Security is a managed detection and response service that combines 24/7 monitoring, expert threat containment, and automation to protect endpoints against cyber threats. Built on SentinelOne’s EDR technology and integrated into Barracuda’s XDR platform, it delivers visibility, behavioral threat detection, and automated response for ransomware, remote code execution, and fileless malware.
Key features include:
- 24/7/365 SOC monitoring: Global security experts continuously monitor endpoint activity and manage threat response
- SentinelOne-powered EDR: Uses AI and behavioral analysis to detect advanced threats like fileless malware, crypto mining, and remote access attacks
- Automated threat response: Pre-configured workflows instantly isolate endpoints, terminate malicious processes, and block threats without admin input
- Expert-led containment: Human analysts assess threat severity and execute tailored containment strategies for accurate, effective response
- Ransomware rollback: Restores compromised endpoints to their pre-attack state in a single click, recovering files and reversing system changes
Source: Barracuda
11. Symantec Endpoint Security Complete

Symantec Endpoint Security (SES) Complete is anintegrated endpoint protection platform that protects against cyber threats across every stage of the attack chain. It combines prevention, detection, response, and threat hunting into a single-agent architecture that supports on-premises, cloud, and hybrid deployments.
Key features include:
- Single-agent, single-console architecture: Simplifies deployment and management while reducing overhead across all environments
- Multi-layered protection: Covers the entire attack chain with integrated prevention, detection, and response capabilities
- Adaptive protection: Automatically customizes security policies to harden endpoints without impacting user productivity
- Cross-platform coverage: Protects major operating systems (Windows, macOS, Linux, iOS, and Android) across desktops, servers, and mobile devices
- Living-off-the-land attack defense: Identifies and blocks abuse of legitimate tools and processes often missed by traditional AV
Source: Symantec
12. Check Point Harmony Endpoint

Check Point Harmony Endpoint is a unified platform that delivers EPP, EDR, and XDR capabilities in a single lightweight client. Designed to defend against cyber threats and data breaches, it offers a full-stack approach to securing endpoints, including desktops, laptops, servers, VDI, and mobile devices.
Key features include:
- All-in-one security agent: Combines EPP, EDR, and XDR in a single client with unified management
- Ransomware and malware protection: Defends against zero-day and known threats using AI-powered ThreatCloud intelligence
- Phishing and browser protection: Prevents zero-phishing attacks without impacting user experience
- Automated posture management: Reduces attack surface through vulnerability assessment and patch management
- Data Loss Prevention (DLP): Protects sensitive data with DLP tools and full disk encryption to maintain compliance
Source: Harmony SASE
How to Choose the Right Endpoint Security Solution
Selecting the right endpoint security solution depends on your workforce model, risk exposure, compliance requirements, and internal security maturity. Organizations should first determine whether their primary challenge is device-level threat protection, secure remote access, BYOD enablement, or a combination of these factors.
When to choose a remote work or BYOD-focused solution
If employees use personal devices or operate in hybrid environments where full device control is not feasible, a secure workspace or BYOD-focused platform may be more appropriate. These solutions isolate corporate data, enforce zero-trust access policies, and protect business applications without intrusive device management. They are especially useful for contractors, distributed teams, or privacy-sensitive environments where installing full EDR agents on personal devices may not be acceptable.
In many cases, organizations deploy both approaches: endpoint security for corporate-managed assets and secure workspace solutions for BYOD users. This layered model ensures strong threat detection while maintaining flexibility for remote work.
When to choose traditional endpoint security (EPP/EDR/XDR)
If your organization manages corporate-owned devices and needs strong threat prevention and incident response capabilities, an endpoint protection platform combined with EDR or XDR is typically the right foundation. These tools focus on detecting malware, ransomware, lateral movement, and advanced persistent threats. They are well suited for environments where devices are centrally managed and security teams require deep visibility and forensic telemetry.
Organizations with mature security operations centers (SOCs) may benefit from EDR or XDR platforms that integrate with SIEM and identity systems. If internal expertise is limited, MDR services can provide 24/7 monitoring and guided response without building a full in-house team.
Key evaluation criteria:
- Coverage across devices and platforms: Ensure compatibility with all operating systems, mobile devices, servers, and virtual environments in your infrastructure.
- Detection and response depth: Assess whether prevention-only controls are sufficient or if behavioral analytics, threat hunting, and automated remediation are required.
- Deployment and management complexity: Cloud-based consoles and lightweight agents simplify rollout and reduce administrative overhead.
- Integration with existing security tools: Strong API support and integration with SIEM, identity, firewall, and email systems improve cross-domain visibility and response coordination.
- Scalability and performance impact: Choose solutions that scale with business growth and do not degrade endpoint performance.
- Automation capabilities: Evaluate automatic containment, rollback, device isolation, and policy enforcement to minimize response time.
- Compliance alignment: Confirm support for encryption, logging, audit trails, and reporting required by regulatory frameworks.
- Cost structure: Compare per-user or per-device pricing with total cost of ownership, including operational and staffing impact.
Conclusion
Endpoint security has evolved beyond traditional antivirus into a multi-layered discipline that combines prevention, detection, response, and centralized management. As organizations support remote work, BYOD, and cloud-driven operations, protecting endpoints requires visibility across devices, strong policy enforcement, and automated threat response. A well-chosen solution should align with business risk, operational complexity, and compliance requirements while maintaining performance and usability across the environment.