SASE Solutions: Key Benefits and 10 Solutions to Know in 2026

What Are Secure Access Service Edge (SASE) Solutions?
Secure Access Service Edge (SASE) solutions, pronounced “sassy,” converge software-defined wide area networking ( SD-WAN ) with comprehensive, cloud-native security, including Zero Trust Network Access (ZTNA), Secure Web Gateways (SWG), Cloud Access Security Brokers (CASB), and Firewall-as-a-Service (FWaaS), into a single, unified, vendor-agnostic service. They secure distributed workforces by delivering consistent security policies to users and devices regardless of location.
Key benefits of SASE:
- Enhanced security: Provides consistent policy enforcement for remote and in-office users, reducing the attack surface.
- Improved performance: Reduces latency by optimizing traffic routing, which is critical for cloud application performance.
- Reduced complexity and cost: Consolidates multiple security point products into one, lowering management overhead and infrastructure costs.
- Agility and flexibility: Enables rapid deployment of security for new users, sites, or services.
By shifting network security from data centers to the cloud, SASE enables organizations to securely connect users, devices, and applications at scale. This model responds to evolving enterprise needs where employees work from anywhere and resources are dispersed across multiple clouds.
Go Beyond SASE: Extend Zero Trust to the Endpoint
Protect network traffic AND endpoint data on unmanaged laptops without latency or IT complexity.
In this article:
Key Benefits of SASE Solutions
Enhanced Security
SASE solutions improve enterprise security by unifying multiple protective technologies into a centralized cloud service. By integrating identity-driven controls, threat detection, malware prevention, data loss prevention, and encrypted traffic inspection, SASE platforms address threats closer to users and devices. Policies are enforced consistently, reducing gaps caused by disjointed legacy products.
As organizations adopt remote work and SaaS applications, the traditional security perimeter dissolves, increasing exposure. SASE provides context-aware, scalable security that adapts to changing risk. Visibility spans users, devices, locations, and applications, helping protect sensitive data and support regulatory requirements.
Improved Performance
SASE improves application and network performance by routing user traffic through a distributed network of cloud-based points of presence (PoPs). This minimizes latency by directing connections over backbone infrastructure instead of forcing traffic through a central data center. Integrated traffic shaping and quality of service features support business applications.
The cloud-native design of SASE supports scaling, bandwidth allocation, and resilience against outages. With dynamic path selection and optimization, users can access applications from corporate offices, branch locations, or remote environments.
Reduced Complexity and Cost
Legacy network and security architectures often rely on separate, appliance-based point solutions managed in silos, leading to inefficiency and high costs. SASE consolidates these functions into a unified platform that is centrally managed and delivered as a service. This reduces hardware, maintenance, and overlapping software subscriptions.
Centralized management reduces the workload on IT teams by minimizing manual updates, inconsistencies, and policy errors. With simplified provisioning and automated scalability, SASE platforms help contain operational expenses.
Agility and Flexibility
SASE allows organizations to adapt to changing business requirements and threat conditions. Cloud-delivered architecture supports on-demand deployment of network and security services without traditional infrastructure rollouts. Organizations can onboard new users, locations, or applications while maintaining compliance and security standards.
The policy engine in SASE supports granular access controls, application segmentation, and dynamic risk mitigation. This supports distributed workforces and cloud adoption without extensive reconfiguration or downtime.
Related content: Read our guide to SASE security (coming soon)
BYOD-Centric SASE Extension Platforms vs. Cloud Native SASE Platforms
BYOD-centric SASE extensions focus on extending secure access to unmanaged or personal devices in remote and hybrid work scenarios. These platforms typically do not replace the enterprise network but create a secure, isolated environment on endpoints. They enforce data loss prevention, application control, and contextual access policies without requiring changes to the user’s personal operating system or infrastructure. This approach is well-suited for organizations that allow bring-your-own-device (BYOD) policies or employ third-party contractors who use their own hardware.
Cloud-native SASE platforms offer a fully integrated networking and security architecture designed to replace legacy WAN and security stacks. They provide global connectivity through private backbones and a full security stack (SWG, ZTNA, CASB, FWaaS) managed from a single cloud-based control plane. These platforms are optimized for performance, scalability, and policy consistency across all user types and device form factors. While BYOD-centric extensions secure the endpoint, cloud-native SASE secures the entire access path from device to application.
Notable SASE Solutions
BYOD-Centric SASE Extension Platforms
1. Venn

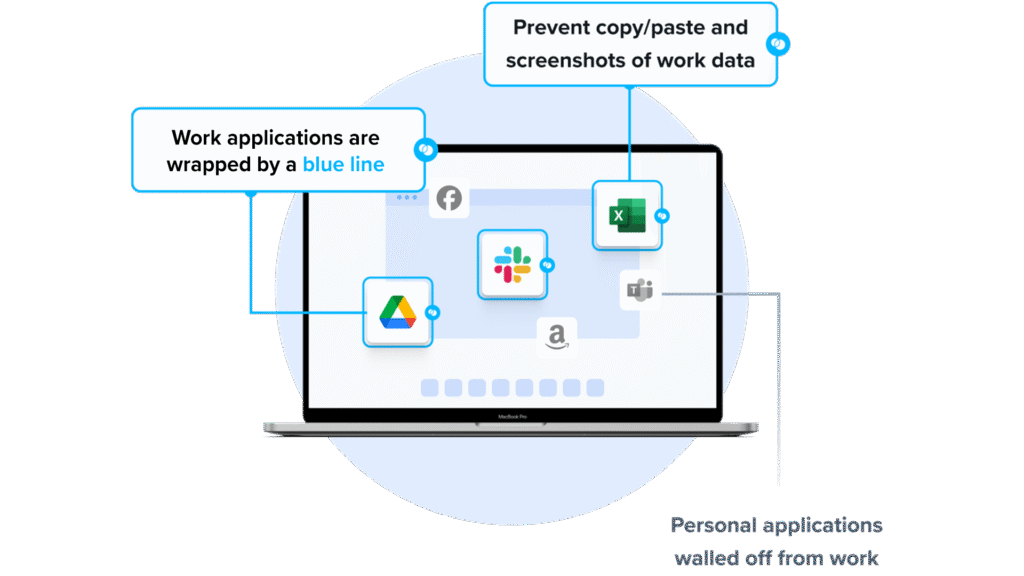
SASE solutions are powerful for securing network traffic, but they weren’t designed to protect data on unmanaged devices. This leaves IT and security teams with a critical gap: sensitive files, local applications, and offline data remain exposed on BYOD laptops and contractor devices. Venn complements existing SASE deployments by securing both network traffic and the work environment directly on the endpoint. Company applications and data are isolated within a secure enclave on the user’s device, ensuring protection across cloud, local, and legacy applications without adding latency or complexity.
Venn’s Blue Border™ provides:
- Full endpoint security: Protects all work apps and data, not just network traffic
- Strong data protection: Prevents file downloads, unauthorized access, and exfiltration
- No performance slowdowns: Runs locally with zero VPN-like latency
- Supports all applications: Cloud, local, and legacy apps remain secure
- Faster deployment & easier management: Lightweight, simple to implement, minimal IT burden
If you want to see Venn in action, book a demo here.
2. ThinScale Secure Remote Worker

ThinScale Secure Remote Worker (SRW) is a software-only SASE extension for securing BYOD and unmanaged Windows endpoints in remote or hybrid environments. It creates a temporary isolated workspace that enforces enterprise security policies without changing the user’s personal system.
Key features include:
- Isolated secure workspace: Runs approved applications in a dedicated environment, blocking access to the base operating system.
- Data loss prevention: Uses BitLocker encryption and virtual storage; disables clipboard, USB, and screen capture.
- USB and application control: Enforces restrictions on device and application usage.
- Fast deployment: Installable on endpoints with minimal setup.
- Access policy enforcement: Checks hardware and network conditions before session start.
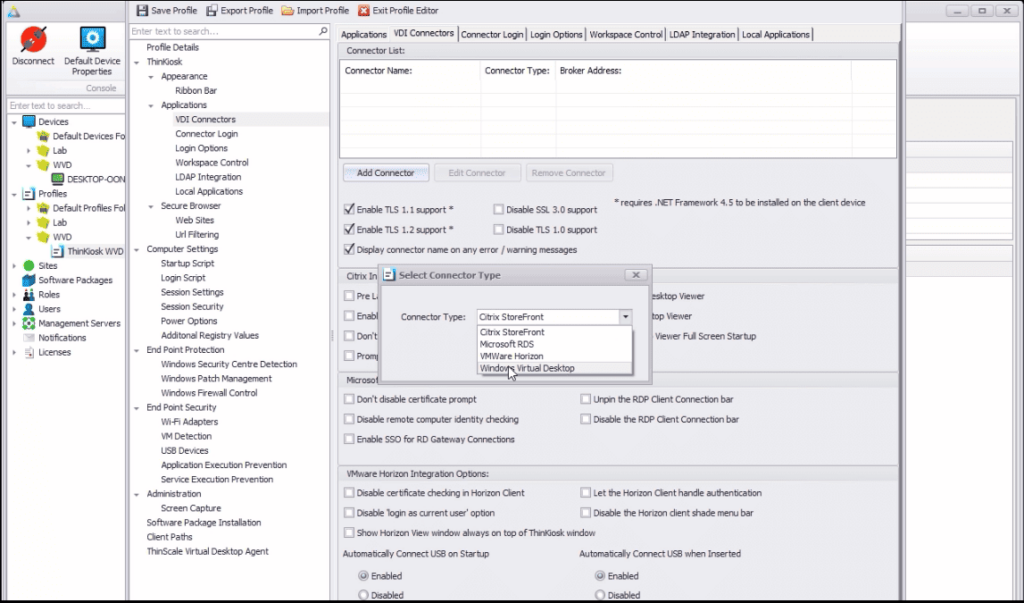
Source: ThinScale SASE
3. IBM MaaS360
IBM MaaS360 is a unified endpoint management (UEM) solution for managing mobile devices, laptops, and tablets from a single platform. It supports hybrid and frontline workforces with automated provisioning, mobile threat defense, and analytics. IBM MaaS360 supports device onboarding, security policy enforcement, and endpoint visibility across environments.
Key features include:
- Unified endpoint management: Central management of mobile devices, laptops, and tablets.
- AI-powered insights: Watson analytics for threat intelligence and automation.
- Built-in mobile threat defense: Detects and remediates device risks.
- Simplified deployment: Automated configuration and setup.
- Automated compliance enforcement: Applies security policies across endpoints.
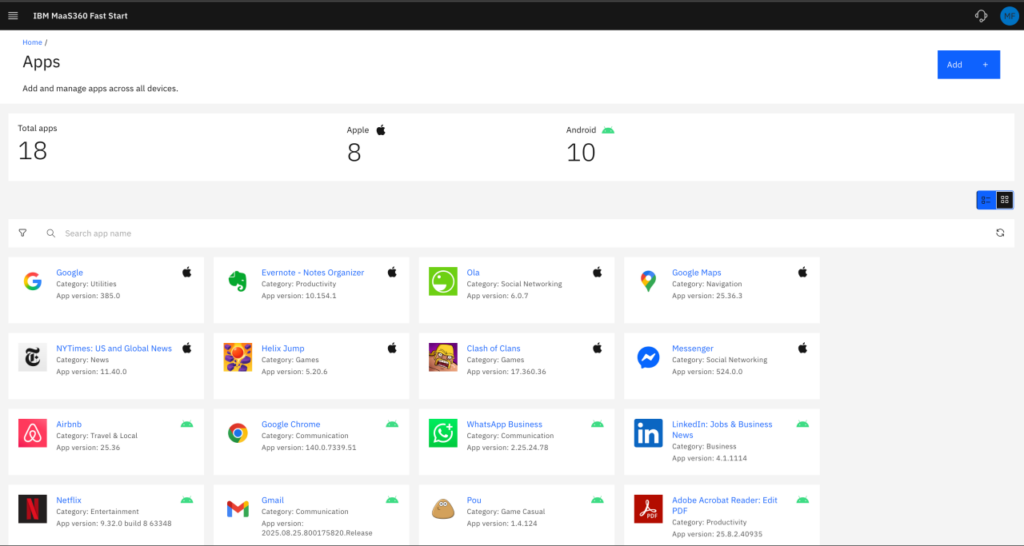
Source: IBM MaaS360
Cloud-Native SASE Platforms
4. Cato SASE Cloud

Cato SASE Cloud is a cloud-native platform that combines networking and security into a global service, connecting users, sites, applications, and cloud resources through a private backbone. It replaces legacy network services and point security tools with SD-WAN, remote access, and cloud security. The platform supports phased adoption without disrupting operations.
Key features include:
- Global private backbone: SLA-backed network of PoPs with encrypted transport and high availability.
- SD-WAN with cloud on-ramps: Cato Socket devices provide resiliency, quality of service, and failover.
- Optimized application performance: Traffic acceleration for SaaS, cloud, and WAN applications.
- Cloud and endpoint security (SSE 360): Integrated firewall, secure web gateway, zero trust access, and endpoint protection.
- Flexible remote access: Client-based and clientless access to private applications.
5. Netskope One SASE

Netskope One SASE is a cloud-native platform that combines security service edge (SSE) with SD-WAN to provide access to users, devices, and applications. It replaces tools such as VPNs, proxies, firewalls, and routers with a single-vendor architecture.
Key features include:
- Unified SSE and SD-WAN: Combines secure access and connectivity in one platform.
- Zero trust architecture: Policies enforce access to private applications, cloud services, and web resources.
- Cloud-native deployment: Uses distributed infrastructure instead of network perimeters.
- High-performance access: Supports connectivity for remote users, branches, and cloud workloads.
- Data protection everywhere: Provides visibility and control over sensitive data.
6. Fortinet FortiSASE
Fortinet FortiSASE is a SASE solution that combines cloud-delivered security with SD-WAN to provide access for remote, branch, and campus environments. It uses a single operating system, client, and data lake to manage policy and operations.
Key features include:
- Unified platform: Single operating system and agent for SD-WAN, SSE, and ZTNA.
- Security stack: Includes SWG, CASB, ZTNA, FWaaS, RBI, SSPM, and SD-WAN.
- AI-powered protection: Threat intelligence from FortiGuard Labs and FortiAI-Assist.
- Flexible connectivity options: Supports agent-based, agentless, and SD-WAN access.
- Global SASE network: PoPs worldwide support low-latency access.
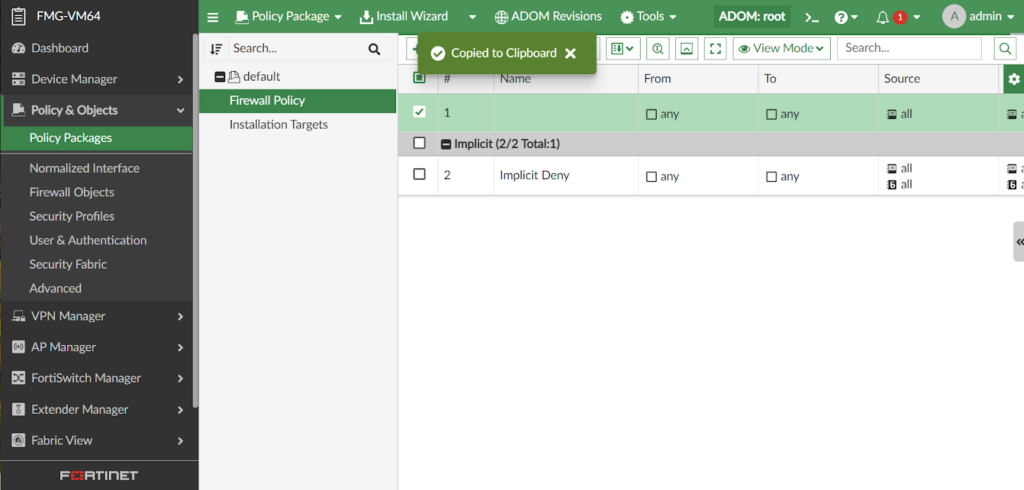
Source: Fortinet
7. Zscaler SASE

Zscaler Zero Trust SASE is a cloud-native solution that unifies networking and security using a zero trust architecture. Built on Zscaler’s SSE platform, it combines zero trust network access with SD-WAN to deliver direct-to-cloud connectivity without exposing internal networks.
Key features include:
- Zero trust-based SD-WAN: Selects traffic paths while reducing lateral movement.
- Secure web gateway (SWG): Inspects and controls internet traffic.
- Cloud access security broker (CASB): Controls cloud application usage and data access.
- Firewall as a service (FWaaS): Provides cloud-delivered firewall capabilities.
- Zero trust network access (ZTNA): Grants access based on identity and context.
Security Platforms With SASE Functionality
8. Cisco Umbrella

Cisco Umbrella, evolving into Cisco Secure Access, is a security service edge (SSE) solution that combines DNS-layer protection with cloud-delivered security services. It secures access to internet, SaaS, and private applications using zero trust principles.
Key features include:
- DNS-layer security: Blocks malicious domains and IP addresses.
- Secure web gateway (SWG): Filters web traffic.
- Cloud access security broker (CASB): Provides visibility and control over cloud applications.
- Firewall as a service (FWaaS): Delivers firewall capabilities without on-prem hardware.
- Data loss prevention (DLP): Protects sensitive information across web and cloud services.
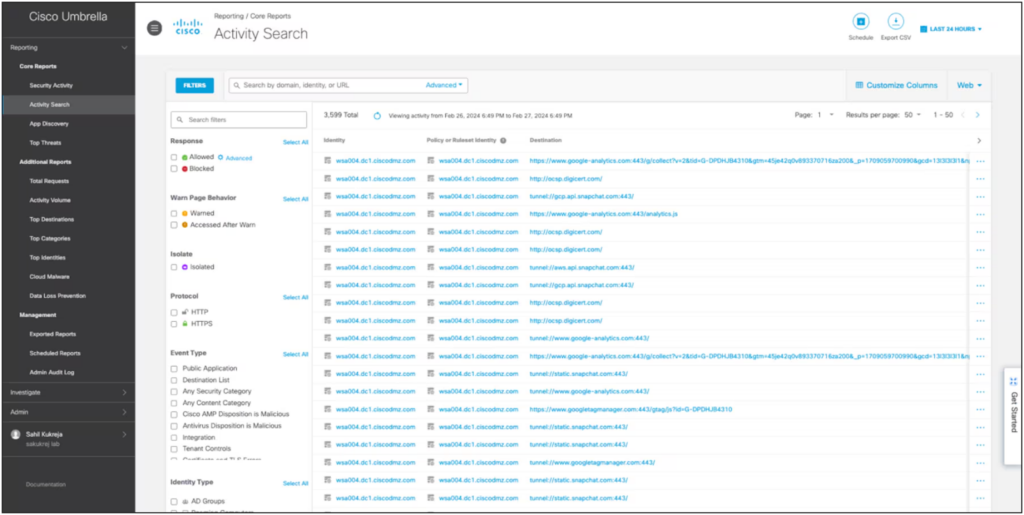
Source: Cisco Umbrella
9. Check Point Harmony SASE

Check Point Harmony SASE is a hybrid SASE platform that combines network security and connectivity in a cloud-based solution. It supports zero trust access, threat prevention, and centralized management across web, SaaS, and private applications.
Key features include:
- Zero trust private access: Identity-based access to applications through a global backbone.
- Hybrid internet access: On-device, browser-based, and cloud protections.
- Secure SD-WAN: Application-aware routing and failover.
- SaaS security: Shadow IT discovery and misconfiguration remediation.
- Mobile device security: Protection for managed and bring-your-own-device endpoints.
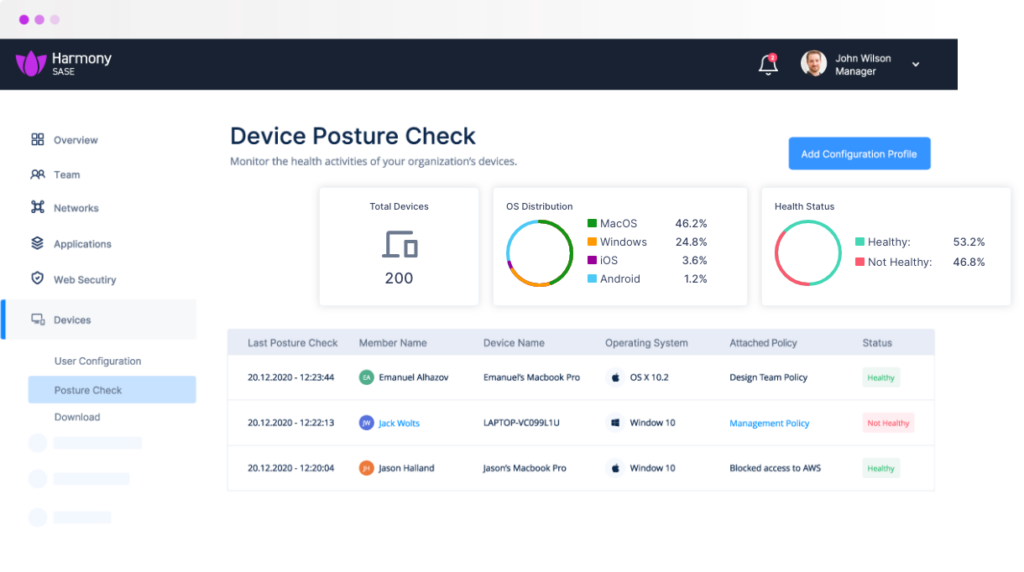
Source: Harmony SASE
10. Cloudflare One

Cloudflare One is a cloud-native SASE platform that combines zero trust security and enterprise networking services on Cloudflare’s global infrastructure. It consolidates security tools and network functions into a single control plane.
Key features include:
- Cloudflare access: Zero trust access control for internal and SaaS applications.
- Cloudflare tunnel: Connects internal resources using outbound encrypted tunnels.
- Secure web gateway (SWG): Filters DNS, HTTP, and network traffic.
- Cloud access security broker (CASB): Monitors SaaS environments for data exposure and misconfigurations.
- Data loss prevention (DLP): Detects and prevents sensitive data exposure.
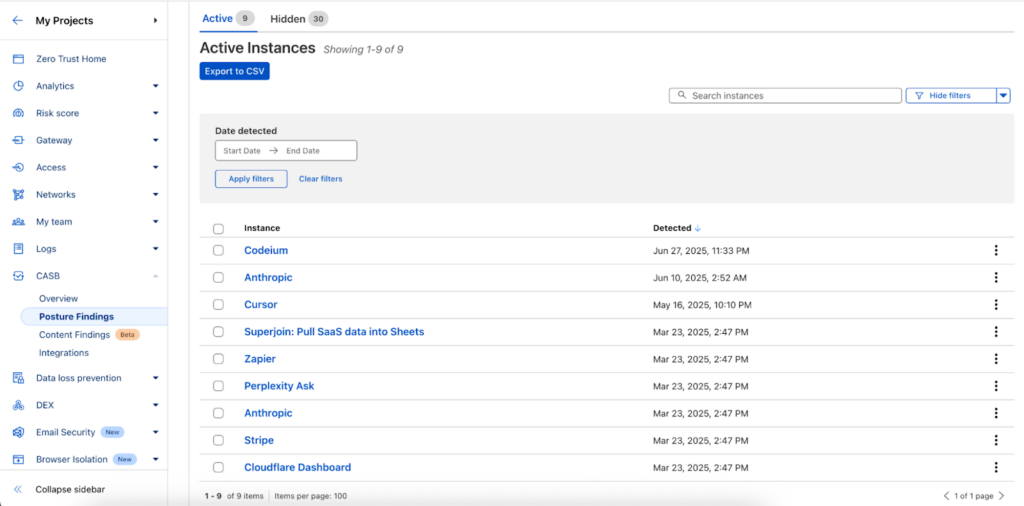
Source: Cloudflare
Evaluating SASE Solutions
Here are some important considerations when selecting a SASE solution.
1. Networking and Security Convergence
A key evaluation criterion for SASE solutions is how networking and security are combined into a unified architecture. This supports consistent policy application and simplifies design by removing separate appliances and management consoles. A SASE solution should provide SD-WAN, firewall, SWG, ZTNA, and CASB with centralized orchestration.
Assessment should also include deployment and update processes, identity integration, policy automation, and cross-service analytics.
2. Zero Trust Enforcement
Zero trust requires continuous authentication and authorization of users, devices, and applications. Evaluation should focus on how ZTNA and contextual access controls are implemented, including least-privilege access, segmentation, and monitoring.
Integration with identity providers, multi-factor authentication, and real-time risk signals are also important considerations.
3. SD-WAN Performance and Optimization
SASE platforms embed SD-WAN to support connectivity for branch offices, remote users, and hybrid cloud environments. Evaluation criteria include WAN optimization, dynamic path selection, failover, and support for MPLS, broadband, and LTE or 5G.
Performance assessment should include latency, jitter, packet loss, scalability, and application-level quality of service.
4. Global Points of Presence (PoPs) and Performance
A provider’s global footprint affects latency and availability. Evaluate the distribution, capacity, and resilience of points of presence. Users should connect to nearby PoPs for application, internet, and cloud access.
Redundancy, failover capabilities, and availability SLAs are important for business continuity. Ensure PoPs support consistent policy enforcement and full security stack inspection to avoid regional security gaps.
5. Unified Management and Visibility
Centralized management is a defining characteristic of SASE. Evaluation should cover dashboards, policy engines, reporting, and API integrations with SIEM or IT service management tools.
Unified management should also support automated provisioning, role-based access, and delegated administration. Look for platforms that provide full visibility into user activity, threat posture, and policy impact in real time.
6. Security Controls and Compliance Support
Security capabilities are not equal among SASE providers. Evaluate each platform’s threat prevention, encryption, data loss prevention, sandboxing, and cloud access security broker features. Compliance support is also key: look for frameworks like GDPR, HIPAA, or PCI DSS, and whether the vendor offers compliance-friendly auditing and reporting.
A strong SASE solution will provide granular, context-aware controls and rapid updates to its security stack, ensuring timely coverage against emerging threats while supporting regulatory adherence. The ability to customize policies for various business units or geographies is also crucial for enterprises operating under multiple compliance mandates.