What Is Zero Trust Network Access (ZTNA)?
Zero Trust Network Access (ZTNA) solutions provide secure, granular, and identity-based access to specific applications, replacing broad-access VPNs with a “never trust, always verify” model. These solutions enhance security by hiding assets from the public internet, using context (user, device, location) to grant least-privilege access, often as part of a SASE framework.
Zero Trust Network Access (ZTNA) is a security framework that assumes no user or device, whether inside or outside the organization’s network, should be trusted by default. Instead of relying on traditional perimeter-based security models, ZTNA enforces strict identity verification and continuous risk assessment before granting access to resources.
Every request to access a system or application is evaluated in real time, leveraging a combination of user identity, device posture, and contextual factors. ZTNA replaces the legacy “castle-and-moat” approach, which often leaves internal resources vulnerable once perimeter defenses are breached. With ZTNA, organizations gain granular control over who can access what, when, and from where.
Implement Zero Trust on Unmanaged Laptops
Discover how to implement zero trust on unmanaged laptops – without VDI or managing the entire device.
In this article:
The Need for ZTNA Solutions
Modern IT environments no longer operate within a clearly defined network perimeter. Applications run in multiple clouds, employees work remotely, and partners require limited access to internal systems. These changes expose weaknesses in traditional security models and create the need for a more adaptive access control approach such as zero trust network access (ZTNA):
- Growth of remote and hybrid work: Employees frequently access corporate resources from home networks, public Wi-Fi, or mobile connections. Traditional perimeter security assumes users are inside a trusted network, which is no longer the case. ZTNA verifies identity and device status for every access request, regardless of location.
- Adoption of cloud and SaaS applications: Many applications now run outside the corporate network in public cloud or SaaS platforms. VPN-based access models struggle to secure these distributed environments. ZTNA provides direct, identity-based access to applications without exposing the broader network.
- Limitations of VPN-based access: VPNs typically grant users broad network access after authentication. If an attacker compromises a VPN account, they may move across internal systems. ZTNA restricts access to only the specified applications or services a user is authorized to reach.
- Reduction of lateral movement: Once attackers enter a network, they often move laterally to locate sensitive systems. ZTNA limits this risk by isolating applications and enforcing least-privilege access. Users can only connect to approved resources rather than the full internal network.
- Increase in device diversity and BYOD: Organizations must support laptops, personal devices, tablets, and mobile phones. These devices may not always meet security standards. ZTNA evaluates device posture, such as patch level or security software, before granting access.
- Need for granular access control: Different users require different levels of access depending on their role. ZTNA allows administrators to define policies based on identity, device health, location, and risk signals.
- Improved visibility and monitoring: ZTNA platforms continuously monitor access sessions and log user activity.
- Support for modern security architectures: Many organizations are adopting security service edge (SSE) or secure access service edge (SASE) architectures. ZTNA is a core component of these models, providing identity-driven access control for distributed users and applications.
Key Components and Features of ZTNA Solutions
Identity and Access Management (IAM)
Identity and access management (IAM) is central to ZTNA, providing the means to authenticate users and manage their access rights. IAM solutions enforce strong authentication methods, such as multi-factor authentication (MFA), to verify user identities before granting access to applications and data. They also integrate with directory services and identity providers to centralize user management and simplify access control.
IAM in ZTNA enables fine-grained access policies based on user roles, group memberships, and other attributes. Organizations can ensure that only authorized users access specific resources, reducing the risk of unauthorized data exposure. IAM also provides audit trails and reporting features that support compliance requirements.
Device Posture and Endpoint Security
ZTNA solutions evaluate the security posture of devices before granting access to corporate resources. This includes checking for updated operating systems, active antivirus software, encrypted storage, and compliance with security policies. By monitoring device health, ZTNA ensures that only trusted and compliant endpoints can connect to sensitive applications.
Endpoint security integration helps address risks from compromised or non-compliant devices. If a device fails posture checks or exhibits suspicious behavior, ZTNA solutions can restrict or revoke its access. This enforcement helps prevent malware, data leaks, and lateral movement by attackers using infected endpoints.
Policy Enforcement Points (PEP)
Policy enforcement points (PEP) are components within a ZTNA architecture responsible for enforcing access decisions in real time. They intercept user requests to applications and resources, evaluate them against defined security policies, and grant or deny access based on the outcome. PEPs are typically deployed at network edges, gateways, or as part of cloud services to ensure consistent enforcement regardless of user location.
ZTNA relies on the scalability of PEPs. These enforcement points support continuous verification, monitoring each session for compliance with security policies and risk signals. If a policy violation is detected during a session, PEPs can revoke access or require re-authentication, minimizing the window of opportunity for attackers.
Application-Level Access Control
Application-level access control in ZTNA restricts user access to only the applications and resources they are authorized to use. Unlike traditional VPNs, which often grant broad network access, ZTNA applies granular controls at the application layer. This limits exposure and reduces the risk of lateral movement by attackers who gain access to the network.
ZTNA solutions map user identities and device postures to application-specific policies. Access to applications is brokered dynamically, with session-level controls and continuous monitoring. This approach improves security and provides direct access to approved applications without complex network configurations or additional client software.
Microsegmentation
Microsegmentation is a technique used in ZTNA to divide the network into smaller, isolated segments, each with its own security controls. By segmenting applications, workloads, and user groups, organizations can contain threats and limit the scope of breaches. Microsegmentation enforces least-privilege access, ensuring users and devices can only communicate with the resources necessary for their roles.
ZTNA uses microsegmentation to implement dynamic, context-aware policies that adapt to changing risk conditions. If a user or device exhibits unusual behavior, access can be restricted to essential segments or revoked. This containment strategy reduces the attack surface and supports regulatory requirements for data segregation and protection.
Context-Aware Access Control
Context-aware access control enhances ZTNA by factoring in real-time context such as user location, device health, time of access, and risk signals when making access decisions. Policies can allow or deny access based on dynamic conditions, for example blocking access from unfamiliar geolocations or requiring additional authentication for high-risk activities.
This adaptive approach balances security and user productivity. Context-aware access control also supports compliance and auditability by providing detailed logs of access decisions and the factors that influenced them.
Related content: Read our guide to zero trust security
Types of ZTNA Solutions
BYOD and Device Enforcement
BYOD-focused ZTNA solutions emphasize securing access from unmanaged or partially managed devices. They enforce policies based on device posture, such as OS version, patch level, encryption status, and presence of security tools, before allowing access to applications.
These solutions often use agent-based or agentless approaches to assess device trust in real time. They enable organizations to safely support personal devices while limiting risk through conditional access, session restrictions, and continuous monitoring of device behavior.
Pure ZTNA Solutions
Pure ZTNA solutions are designed specifically to deliver identity-based, application-level access without relying on legacy VPN infrastructure. They provide direct-to-application connectivity through secure brokers, ensuring that users only access explicitly authorized services rather than the broader network.
These platforms are typically cloud-native and integrate tightly with identity providers, enabling scalable policy enforcement across distributed environments. While they offer strong security and simplified access control, they may require integration effort when replacing existing VPNs or supporting legacy applications.
Notable ZTNA Solutions
BYOD and Device Enforcement
1. Venn

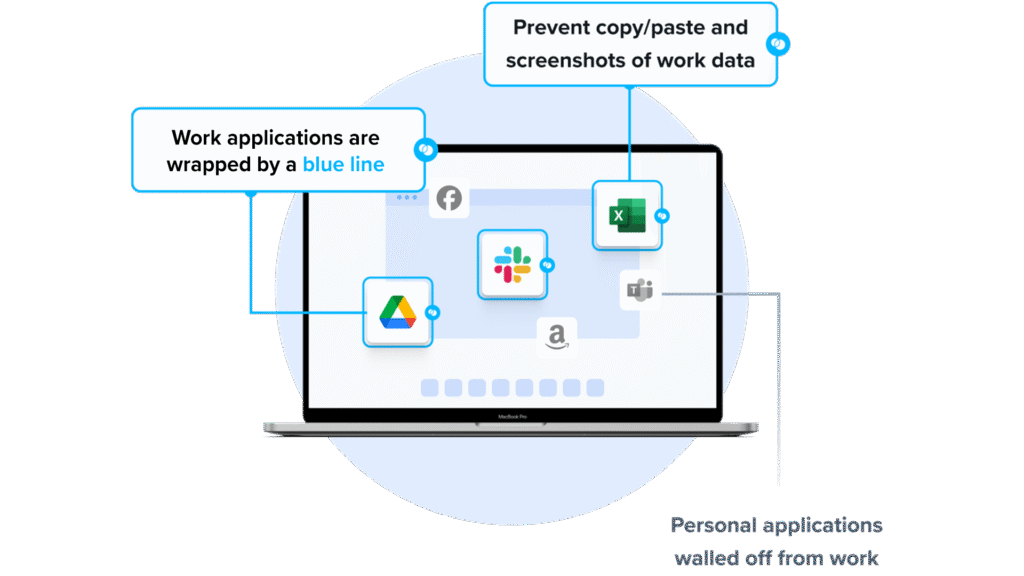
Venn brings zero trust security to remote and BYOD environments by containing company apps and data inside a secure, isolated workspace on any PC or Mac. Instead of relying on traditional VPNs, VDI, or MDM, Venn enforces Zero Trust principles directly on the endpoint — ensuring that every user, device, and action is verified, and company resources are never left exposed.
Similar to an MDM solution but for laptops – work lives in a company-controlled Secure Enclave installed on the user’s PC or Mac, where all data is encrypted and access is managed. Work applications run locally within the Enclave – visually indicated by Venn’s Blue Border™ – protecting and isolating business activity while ensuring end-user privacy.
Zero Trust and BYOD security in Action with Venn:
- Seamless MFA integration – Works with Okta, Azure, and Duo for strong identity verification
- Encrypted workspace – Ensures all corporate apps and data are secured in transit and at rest
- Context-aware access controls – Policies adapt by user, device health, and environment
- Unified Zero Trust platform – Endpoint security, remote access, and Zero Trust enforcement in one
- Faster, scalable alternative – Delivers superior performance compared to legacy VDI
2. Workspace ONE

Workspace ONE provides unified endpoint management that helps organizations control and secure devices used to access corporate applications. The platform manages desktops, mobile devices, and other endpoints across operating systems such as Windows, macOS, iOS, Android, Linux, and ChromeOS from a single cloud-based console.
Key features include:
- Unified endpoint management: Manage desktops, mobile devices, rugged devices, and other endpoints across major operating systems from a centralized console.
- Conditional access policies: Enforce access decisions based on device compliance, user role, and risk signals.
- Device posture and compliance checks: Verify device security status before allowing access to corporate resources.
- Low-touch remote onboarding: Automate device enrollment and configuration.
- App lifecycle management: Deploy, update, and manage applications across multiple device types from one platform.
Source: Workspace One
3. Citrix Device Posture
Citrix Device Posture is a cloud-based service that verifies the security status of endpoint devices before allowing users to access Citrix resources such as Citrix DaaS (virtual apps and desktops) and Citrix Secure Private Access applications. The service supports zero trust principles by evaluating whether a device meets predefined security policies before login.
Key features include:
- Device posture verification: Evaluates endpoint security conditions before allowing access to corporate applications or virtual desktops.
- Zero trust enforcement: Ensures devices meet defined compliance requirements before users can log in to Citrix environments.
- Policy-based access control: Administrators define posture policies that determine whether a device is allowed or denied access.
- Device classification: Devices are categorized as compliant, non-compliant, or denied login depending on policy results.
- Granular access restrictions: Non-compliant devices can receive limited access to specified applications or delivery groups.
Source: Citrix Device Posture
Pure ZTNA Solutions
4. Google BeyondCorp Enterprise

Google BeyondCorp Enterprise is a zero trust access solution that shifts security controls from the traditional network perimeter to individual users and their devices. Instead of relying on VPN-based access, it evaluates identity, device security, and contextual signals before allowing users to access enterprise applications. The model enables employees to work securely from untrusted networks while maintaining authentication, authorization, and encrypted connections.
Key features include:
- Zero trust access model: Grants application access based on user identity, device status, and contextual factors rather than network location.
- VPN-less secure access: Allows users to access corporate applications from untrusted networks without requiring a traditional VPN.
- User and device authentication: Verifies both user identity and device security posture before granting access to enterprise resources.
- Context-aware access policies: Access decisions consider factors such as user credentials and device characteristics.
- Single sign-on (SSO): Provides centralized authentication for multiple applications and services.
5. Twingate

Twingate is a ZTNA platform that provides secure remote access to internal applications and infrastructure without exposing the corporate network. It connects users directly to specific resources using identity-based access controls and device security checks. The platform enforces least-privilege access by verifying user identity, device posture, and contextual factors before allowing connections.
Key features include:
- Identity-first access control: Uses identity provider integrations to authenticate users and manage authorization to specific resources.
- Granular resource-level access: Grants users access only to approved applications or services rather than the entire network.
- Device posture enforcement: Validates device security conditions with built-in checks and integrations with MDM and EDR solutions.
- Multi-factor authentication support: Enables MFA methods such as TOTP, biometrics, and security keys for secure access to services like SSH and RDP.
- No open inbound ports: Uses outbound-only connections through connectors.
Source: TwinGate
6. Cyolo

Cyolo PRO (Privileged Remote Operations) is a secure remote access solution that provides identity-based connectivity to critical systems, particularly in operational technology (OT) and cyber-physical system (CPS) environments. The platform enables organizations to grant secure access to industrial assets without modifying existing infrastructure or network architecture.
Key features include:
- Identity-based authentication: Enforces secure access using modern identity controls such as multi-factor authentication and identity verification.
- Zero trust remote access: Applies least-privilege principles to ensure users only access authorized systems and applications.
- Flexible deployment options: Supports deployment in on-premises, cloud-connected, or fully isolated environments.
- Legacy system support: Adds modern authentication, credential vaulting, and password rotation to legacy OT systems without infrastructure changes.
- Granular access policies: Allows administrators to define access controls based on user roles, applications, time, or location.
Source: Cyclo
7. NordLayer

NordLayer is a network security platform that implements ZTNA to control how users connect to applications, devices, and internal resources. Instead of trusting users based on network location, NordLayer verifies identity, context, and policy compliance before granting access. The platform acts as a trust broker that evaluates each access request and enforces defined security policies.
Key features include:
- Zero trust access control: Verifies user identity and context before allowing connections to applications or network resources.
- Identity-based security policies: Defines access rules based on user roles, permissions, and organizational requirements.
- Secure cloud access: Restricts and manages access to cloud infrastructure and applications according to defined policies.
- Network segmentation: Separates internal resources into controlled segments to reduce exposure and limit unauthorized movement.
- Least-privilege access enforcement: Ensures users can only access the applications and data necessary for their roles.
Source: NordLayer
8. Appgate ZTNA

Appgate ZTNA uses a direct-routed architecture to connect users, devices, and workloads to authorized resources without sending traffic through a vendor-hosted cloud proxy. This approach gives organizations more control over how traffic moves across their environment while supporting identity-centric, least-privilege access policies.
Key features include:
- Direct-routed access: Connects users directly to authorized resources without forcing traffic through a third-party cloud.
- Identity-centric zero trust control: Applies access decisions based on identity and least-privilege principles.
- Reduced attack surface: Cloaks resources from unauthorized users to make internal systems less visible to attackers.
- Lateral movement prevention: Limits access to only approved resources to reduce the spread of threats inside the environment.
- Low-latency connectivity: Improves performance by avoiding indirect traffic routing and cloud detours.
Source: AppGate
Related content: Read our guide to zero trust solutions
Conclusion
ZTNA represents a shift from network-centric security to identity- and context-driven access control, enabling organizations to secure applications in distributed environments. By enforcing least-privilege access, continuously verifying trust, and isolating resources, ZTNA reduces attack surface and limits the impact of compromised credentials or devices.