Featured Resources
How to Create a BYOD-Friendly Data Loss Prevention Policy


March 13, 2025
Blog
How to Create a BYOD-Friendly Data Loss Prevention Policy
Creating and implementing a data loss prevention policy is a critical security measure for organizations today. But many DLP policies prioritize security at the cost of usability, which leads to employee frustration and, in turn, security workarounds–ultimately increasing the risk of data leaks and shadow IT. Achieving this balance is challenging, as implementing DLP policies […]
BYOD Security: Managing Third-Party Risk


February 18, 2025
Blog
BYOD Security: Managing Third-Party Risk
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency


December 17, 2024
Blog
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency
5 Myths About Remote Work Security: What Every IT Leader Should Know


June 12, 2024
Blog
5 Myths About Remote Work Security: What Every IT Leader Should Know
What Is Data Loss Prevention? Technologies and Best Practices in 2025


Knowledge Article
What Is Data Loss Prevention? Technologies and Best Practices in 2025
What Is Data Loss Prevention (DLP)? DLP refers to Data Loss Prevention, a set of tools and processes used by organizations to prevent sensitive data from being leaked, stolen, or misused. DLP solutions work by identifying, monitoring, and protecting sensitive data in motion, at rest, and in use across an organization’s IT infrastructure, helping to […]
Best Browser Security Software: Top 5 Options in 2025


Knowledge Article
Best Browser Security Software: Top 5 Options in 2025
What Is Browser Security Software? Browser security software protects users and organizations from threats during web browsing. Unlike legacy antivirus or network security solutions, browser security software focuses on threats from web content, web applications, and browser plugins. Common risks include phishing attacks, drive-by downloads, malicious extensions, and data breaches from compromised web sessions. As […]
Jamf for BYOD: Features, Pricing, Limitations and Alternatives


Knowledge Article
Jamf for BYOD: Features, Pricing, Limitations and Alternatives
What Is Jamf? Jamf is a software platform that helps organizations manage Apple devices across their workforce. It provides tools for deploying, configuring, and securing iOS, macOS, iPadOS, and tvOS devices at scale. By using Jamf, IT teams can remotely configure settings, deploy applications, enforce security policies, and track device health from a centralized dashboard. […]
Best Browser Security Solutions: Top 5 Providers in 2025


Knowledge Article
Best Browser Security Solutions: Top 5 Providers in 2025
What Are Browser Security Solutions? Browser security solutions include remote work solutions like Venn and dedicated enterprise browsers like Island. These are enterprise-focused platforms that protect against browser-based threats like malware, phishing, and data leaks, by employing features such as sandboxing, real-time threat detection, granular policy enforcement, and the separation of work and personal activities. […]
Building a Successful BYOD POC: An Intro Guide for IT Leaders


September 17, 2025
Blog
Building a Successful BYOD POC: An Intro Guide for IT Leaders
Eliminating Complexity in the Era of Remote Work The rapid expansion of remote and distributed workforces is forcing IT teams to rethink how they scale operations. Traditional approaches – provisioning, shipping, and managing company-owned laptops or standing up costly, complex VDI deployments – are creating bottlenecks that slow down productivity and drain budgets. To keep […]
5 Risks of Unmanaged Devices and How to Mitigate Them


Knowledge Article
5 Risks of Unmanaged Devices and How to Mitigate Them
What Are Unmanaged Devices? Unmanaged devices are network-connected devices that lack active monitoring, management, or control by IT or security teams. They are often personal devices or third-party devices that employees or contractors use, which fall outside of the organization’s standard management and security policies. These devices can pose significant security risks due to lack […]
Mobile Application Management (MAM): Challenges and Best Practices


Knowledge Article
Mobile Application Management (MAM): Challenges and Best Practices
What Is Mobile Application Management (MAM)? Mobile Application Management (MAM) is a security framework focused on controlling and securing mobile applications within an organization. It allows IT administrators to manage and protect corporate data within apps on both company-owned and personal devices, without necessarily managing the entire device. MAM solutions handle app distribution, configuration, access […]
8-Step Process for Contractor Onboarding Success


Knowledge Article
8-Step Process for Contractor Onboarding Success
What Is Contractor Onboarding? Contractor onboarding is the process of integrating independent contractors or freelancers into a company, ensuring they understand their roles, responsibilities, and how to work effectively within the organization. This process differs from employee onboarding and focuses on legal compliance, clear communication, and efficient access to necessary tools and resources. This onboarding […]
Enforce DLP Policies for Installed Apps on Unmanaged or BYOD Computers
September 11, 2025
Product Demos
Enforce DLP Policies for Installed Apps on Unmanaged or BYOD Computers
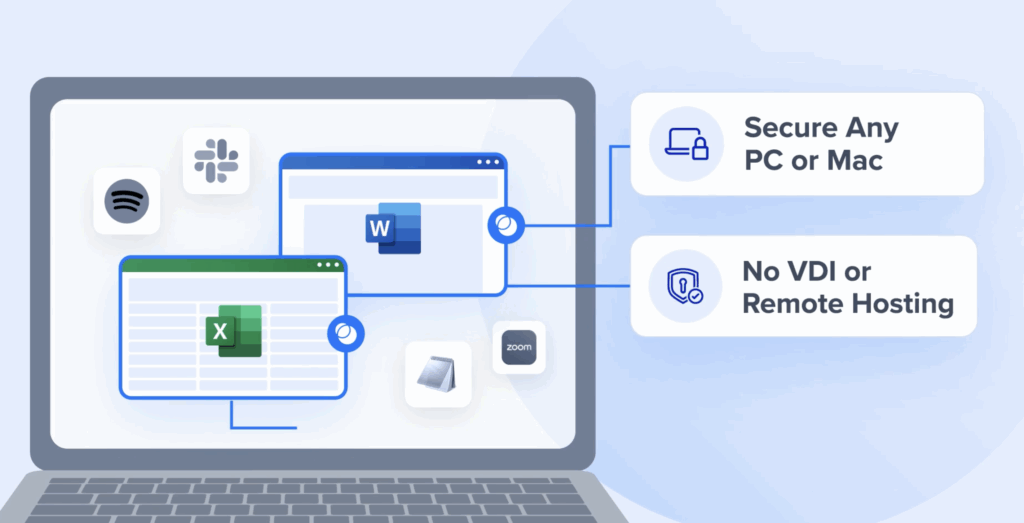
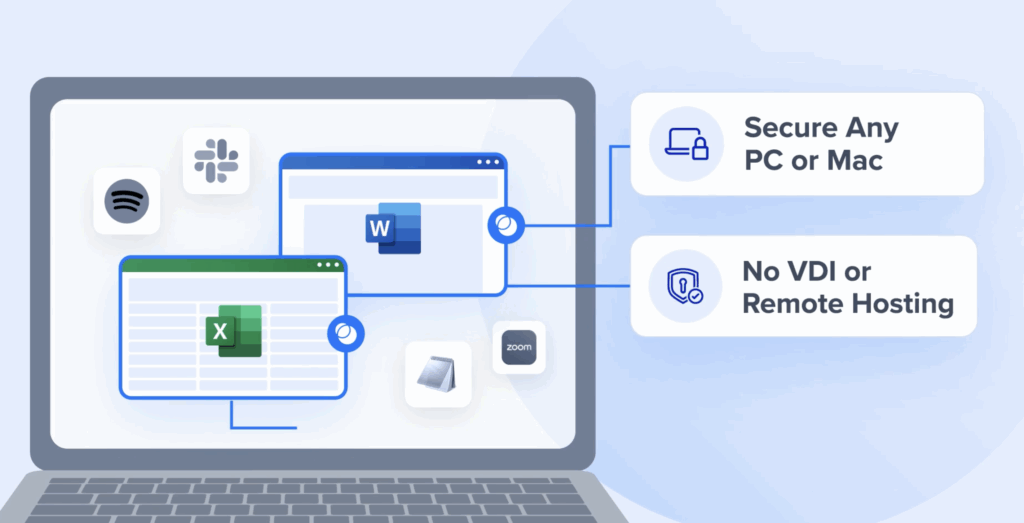
Today’s workforces aren’t just full-time employees sitting in the office. Contractors, consultants, and remote employees are a critical part of many organizations, but giving them secure access to company data isn’t easy. Personal devices, unmanaged laptops, and diverse software environments create real security challenges, especially when sensitive data is involved. Traditional solutions, like virtual desktops […]