Featured Resources
How to Create a BYOD-Friendly Data Loss Prevention Policy


March 13, 2025
Blog
How to Create a BYOD-Friendly Data Loss Prevention Policy
Creating and implementing a data loss prevention policy is a critical security measure for organizations today. But many DLP policies prioritize security at the cost of usability, which leads to employee frustration and, in turn, security workarounds–ultimately increasing the risk of data leaks and shadow IT. Achieving this balance is challenging, as implementing DLP policies […]
BYOD Security: Managing Third-Party Risk


February 18, 2025
Blog
BYOD Security: Managing Third-Party Risk
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency


December 17, 2024
Blog
How a Call Center-Driven Healthcare Company is Tackling BYOD and Operational Efficiency
5 Myths About Remote Work Security: What Every IT Leader Should Know


June 12, 2024
Blog
5 Myths About Remote Work Security: What Every IT Leader Should Know
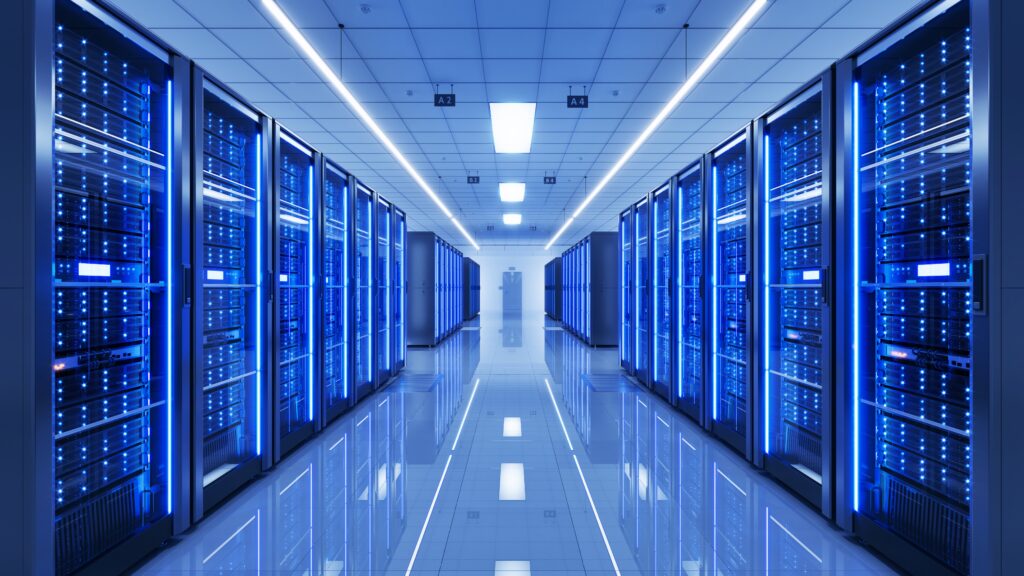
What is VDI? Virtual Desktop Infrastructure
Knowledge Article
What is VDI? Virtual Desktop Infrastructure
Virtual desktop infrastructure (VDI), a software solution that uses virtualization technology to provide remote access to a virtual, hosted desktop, simplifies the process of supporting and securing a remote workforce. VDI uses virtualization technology to create virtual desktops that are hosted within a corporate data center or cloud environment and are remotely accessible to a […]
BYOPC: What is Bring Your Own Personal Computer?


Knowledge Article
BYOPC: What is Bring Your Own Personal Computer?
The rise of remote and hybrid work has driven new technological trends, and among these is Bring Your Own PC (BYOPC), which is a subset of Bring Your Own Device(BYOD). BYOPC Security programs, according to Gartner, permit personally purchased client devices to execute enterprise applications and access company data. What is BYOPC? BYOPC is a logical […]
SASE vs Zero Trust: How they Work Together


Knowledge Article
SASE vs Zero Trust: How they Work Together
The zero-trust security model was developed in response to the evolution of corporate infrastructure and cybersecurity risk. In the past, companies widely adopted a perimeter-focused security model designed to prevent external attackers from gaining access to the protected internal network. As companies increasingly embrace cloud computing, traditional perimeter-focused security models no longer make sense, especially […]
VDI Security Risks and Best Practices


Knowledge Article
VDI Security Risks and Best Practices
Companies with a remote workforce or with third-party contractors can experience significant logistical and security challenges. Remote workers may use personal devices under a bring-your-own-device (BYOD) or bring-your-own-PC (BYO-PC) program, which may not be compatible with corporate applications. Companies also face data security challenges, including ensuring that sensitive corporate data accessible to remote workers is […]
What is Secure Remote Access Control?


Knowledge Article
What is Secure Remote Access Control?
In recent years, organizations are increasingly embracing remote and hybrid work models; however, these work arrangements can carry significant cybersecurity risks. Secure remote access solutions help an organization to manage the risks of a remote work program by reducing the risk of data loss, compromised systems, and other threats to the business. This is part […]
Ensuring Data Security When Employees Work Remotely


December 14, 2023
Blog
Ensuring Data Security When Employees Work Remotely
Remote work skyrocketed out of necessity during the pandemic. Pew Research Center reports that the percentage of remote workers stands at 35%, less than the high of 55% in October 2020, but dramatically above pre-pandemic levels of 7%. Much of this may be due to the fact that organizations that offer remote or hybrid work […]
VDI is Legacy: For Securing Remote Workers, the Future is Local


eBook
VDI is Legacy: For Securing Remote Workers, the Future is Local
Modern remote work has eroded the promise of virtual desktops. IT and security teams are increasingly recognizing VDI as a less-than-ideal choice due to its high costs, complexity, and latency. The future of secure remote work requires a ‘local’ solution that is seamless and intuitive. What You Will Learn The only way to overcome the […]
Webinar: How to Overcome At-Home Agent Onboarding While Reducing Costs and IT Headaches


Webinar
Webinar: How to Overcome At-Home Agent Onboarding While Reducing Costs and IT Headaches
Enhance Security with Venn: Secure Access to Web Apps (Video)


November 16, 2023
Product Demos
Enhance Security with Venn: Secure Access to Web Apps (Video)
Venn provides secure access to web apps by isolating the work browser in a secure enclave and limiting access to SAS applications through VPN, Sassy, or the company’s gateway. By implementing IP restrictions, it prevents access to SAS apps outside the enclave, ensuring sensitive data remains within the secure perimeter. An example of the effectiveness […]