Why VDI is Dead: A Eulogy for Legacy Remote Work Infrastructure

IT teams have spent years managing the sprawling infrastructure that VDI demands: the servers, the licensing costs, the endless patching cycles, the performance complaints. And yet, many organizations are still holding on. This blog is a summary of our eBook, “VDI is Dead: A Eulogy,” which makes the case that the era of virtual desktops is over, and lays out a blueprint for what comes next.
VDI Had Its Moment
When VDI emerged in the early 2000s, the pitch was compelling: centralized control, simplified device management, and secure remote access from anywhere. For a world built around managed endpoints and on-prem applications, it worked. But the workforce has fundamentally changed, and VDI hasn’t kept up.
The Hidden Costs Are Catching Up
Running VDI reliably isn’t a one-time investment; it’s a continuous operational burden.
High-performance servers, storage arrays, and bandwidth requirements scale with demand. Licensing costs have ballooned, with some organizations seeing increases of up to tenfold over 18 months as vendors restructure into subscription tiers. And beyond the infrastructure, VDI requires specialized headcount to manage it all: virtualization architects, storage admins, network engineers. That “human tax” rarely makes it into the original business case.
Security Assumptions That No Longer Hold
VDI was designed to keep data off the endpoint by remotely hosting everything, but that architecture creates its own risks.
A centralized environment means a single successful exploit can unlock sweeping access across the entire infrastructure, making it a high-value target. Meanwhile, poor user experience drives shadow IT: employees who can’t work efficiently within corporate systems find workarounds, expanding the attack surface in ways that are harder to detect and control.
The Workforce Has Changed. VDI Hasn’t.
Today’s IT teams aren’t governing a uniform fleet of company-issued laptops. They’re managing a mix of:
- managed devices
- BYOD employees
- contractors
- consultants
- offshore teams
All working from devices and networks outside IT’s direct control. VDI was never designed for this level of diversity. The result is fragile architecture that buckles under inconsistent conditions and can’t scale efficiently to meet the reality of how modern organizations operate.
The Alternatives: What Works and What Doesn’t
As frustration with VDI has grown, organizations have turned to VPNs, SASE, enterprise browsers, UEM, and MDM. Each of these addresses parts of the problem, but none delivers a complete answer for BYOD and unmanaged device environments.
The eBook breaks down where each falls short across security, privacy, user experience, and application support.
A New Category: Endpoint Access Isolation
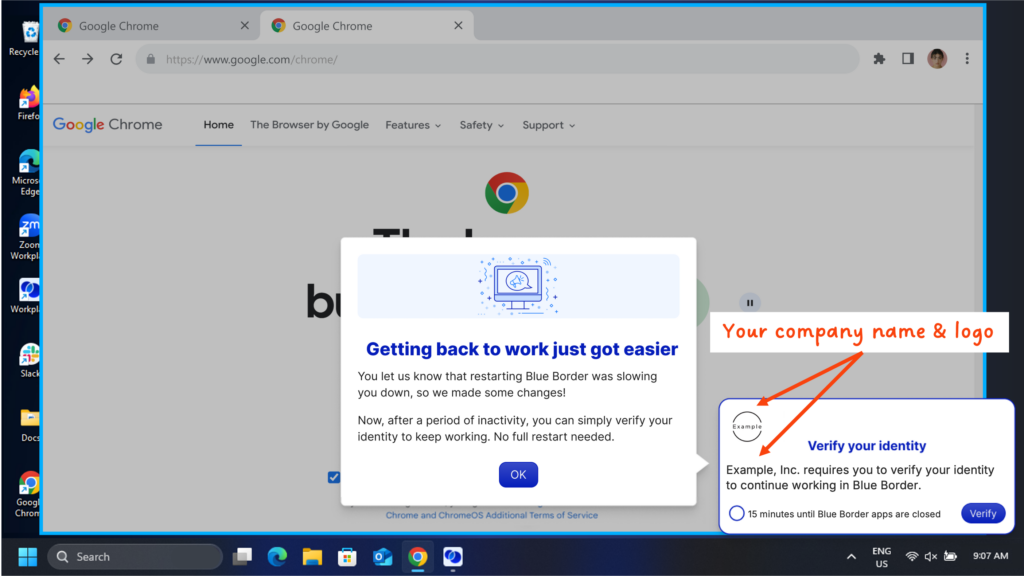
According to Gartner’s Hype Cycle for Workspace Security, 2025, Endpoint Access Isolation (EAI) is emerging as the purpose-built answer. Rather than routing sessions through centralized infrastructure, EAI isolates the work environment locally on the device — delivering native app performance, strong data controls, and continuous authentication without the overhead of VDI. It’s faster to deploy, lighter to maintain, and purpose-built for BYOD and contractor-heavy workforces.
What Organizations Are Doing Instead
The eBook features four real-world examples of organizations that replaced VDI with Blue Border™:
- A BPO that went from days of onboarding per agent to minutes, without sacrificing security
- A financial services firm that cut costs by 40% while maintaining compliance
- A telehealth organization that eliminated VDI lag and improved clinician and patient experience overnight
- A distributed law firm that enabled contractors to work securely from personal laptops without complex setup or device issuance
The Takeaway
VDI served the era it was built for. But in a SaaS-first, BYOD-driven world where contractors and remote workers are the norm, it’s become an anchor — costly, fragile, and mismatched to how work actually happens today. The principles VDI championed (centralized policy, data protection, compliance) still matter. They just need to live closer to the user and the device.
You can read the full eBook here.
Related Guides:
Ronnie Shvueli
Senior Digital Content Marketing Manager
More Blogs